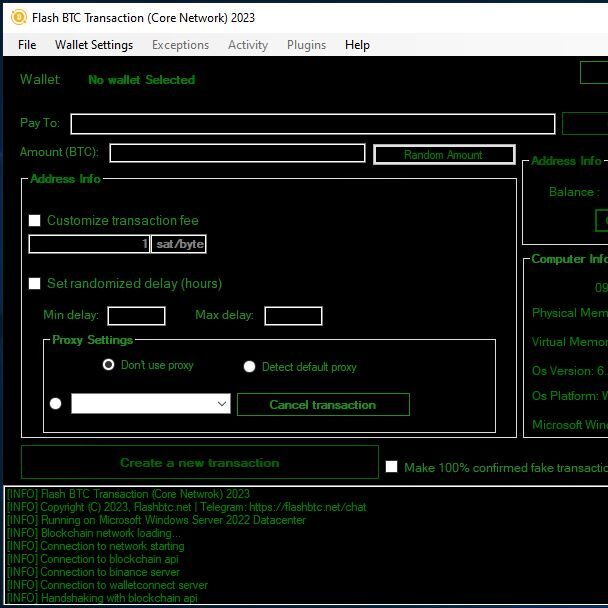
Did you know that using a lost wallet finder could save you from losing millions? Over $7.7 billion was lost to cryptocurrency scams in 2021 alone, with fake Bitcoin transactions representing a significant portion of these losses. For more info on flash btc visit https://realflashbtc.net.
In fact, address poisoning attacks have resulted in over 270 million attempts across Ethereum and BNB Chain, with confirmed losses of $83 million. Additionally, scammers are constantly finding new ways to steal your money through cryptocurrency, making investment scams one of the top methods they use. Even popular tools like WalletConnect have been targeted, with attackers stealing over $580,000 in a single campaign in 2024.
This is why knowing how to identify fake Bitcoin wallets is crucial for anyone involved in crypto. Throughout this guide, we’ll show you how to spot the warning signs of fake wallets and how to use a lost bitcoin wallet finder to protect your assets. Whether you’re concerned about a lost crypto wallet finder’s legitimacy or looking for a reliable lost wallet finder app, we’ve got you covered with practical tips to keep your digital assets safe.
What Is a Fake Bitcoin Wallet?
A fake Bitcoin wallet is a malicious application, website, or digital tool designed to look like a legitimate cryptocurrency wallet but with hidden code that steals users’ funds or personal information. Unlike genuine wallets that securely store your digital assets, fake wallets create a backdoor for fraudsters.
How fake wallets differ from real ones
The most dangerous aspect of counterfeit wallets is how convincingly they mimic legitimate services. These imposters typically:
- Appear visually identical to trusted wallets, complete with copied branding, logos, and user interfaces
- Lack essential security features while maintaining a polished, professional appearance
- Harvest private keys and seed phrases rather than protecting them
- Create seemingly valid wallet addresses that actually redirect funds to scammer-controlled accounts
- Contain malware designed to siphon off cryptocurrency or steal sensitive information
Fake wallets come in multiple forms. Hot wallets (those connected to the internet) are primarily targeted through malicious apps, while cold wallets (hardware devices) might be counterfeited and sold through unofficial channels. Researchers have identified 249 fake cryptocurrency wallet apps across Android and iOS platforms, resulting in stolen funds worth over $4.30 million.
Furthermore, both sophisticated and amateur scammers develop these deceptive tools. Modern fake wallet apps are often nearly indistinguishable from genuine ones, making detection increasingly difficult. Consequently, even experienced cryptocurrency users can fall victim to these schemes.
Why scammers create fake wallets
The primary motivation behind fake wallet creation is straightforward: financial gain through theft. Notably, cryptocurrency transactions are irreversible, making this type of fraud particularly attractive to criminals. Once funds are stolen, recovery becomes virtually impossible.
Scammers employ various sophisticated techniques to distribute their fake wallets:
First, they purchase sponsored ads on search engines and social media to promote their malicious applications. Subsequently, they manipulate app store ratings through fake reviews and artificial download numbers to appear legitimate. Meanwhile, they monitor forums and social platforms, impersonating support staff to convince users to share sensitive wallet information.
The cryptocurrency environment provides abundant opportunities for theft due to several factors. Primarily, many users lack sufficient knowledge about securely navigating this unregulated space. Additionally, fake wallets exploit the fact that cryptocurrency addresses are complex strings of characters that most people can’t verify visually.
Using a counterfeit wallet exposes you to serious risks, including unauthorized access to your funds and complete asset loss. Some fake wallets operate as phishing tools, collecting your private keys and passwords, while others function temporarily before preventing withdrawals once significant deposits are made.
For protection, a lost wallet finder tool can help verify the authenticity of wallet addresses before making transactions. Such verification tools cross-check addresses against known scammer databases, reducing the risk of sending funds to fraudulent destinations.
Common Signs of a Fake Wallet
Spotting a fake Bitcoin wallet requires vigilance and attention to detail. Scammers have become increasingly sophisticated in their methods, creating counterfeit wallets that closely resemble legitimate ones. Fortunately, several telltale signs can help you identify these fraudulent tools before they compromise your assets.
Unverified app sources or websites
The source of your wallet application is perhaps the most critical indicator of its legitimacy. Reputable crypto wallets are distributed through official channels that maintain strict security standards.
Always download wallets exclusively from official links listed on verified project pages or GitHub repositories. Applications distributed outside the official Google Play Store or Apple App Store come with significant risks, as they bypass the security screening processes these platforms enforce.
Scammers frequently use SMS messages or social media posts to distribute links to counterfeit wallet applications. These messages often create a false sense of urgency or offer promotions that seem too good to be true. Remember that legitimate wallet providers rarely solicit downloads through unsolicited messages.
When examining a wallet’s source:
- Carefully verify the domain name before downloading
- Check for PGP signatures or file hashes that match official releases
- Avoid links shared through advertisements, forums, or direct messages
Missing security features like 2FA
Legitimate Bitcoin wallets prioritize security through multiple protective layers. The absence of these features often indicates a fraudulent application.
Two-Factor Authentication (2FA) stands as one of the most essential security measures in cryptocurrency wallets. This feature requires both your password and a second verification method (typically a code sent to your phone) to access your account. When a wallet application doesn’t offer 2FA, consider it a significant red flag.
Likewise, authentic wallets typically include additional security features such as:
- Transaction risk assessment tools (like Trust Wallet’s Security Scanner)
- Robust password requirements
- Biometric authentication options
- Automatic logout after periods of inactivity
Never share your private keys with anyone under any circumstances, as this provides direct access to your cryptocurrency. Legitimate wallets will never ask you to share this information, even for troubleshooting purposes.
Mismatch in wallet address formats
Each cryptocurrency network uses specific address formats, making address validation a powerful method for identifying fraudulent wallets.
The “invalid address” error appears when an address doesn’t match the expected network format. This mismatch sometimes occurs naturally when attempting cross-network transactions, yet it can also indicate a fraudulent wallet attempting to redirect your funds.
For Bitcoin specifically, legitimate addresses typically start with:
- 1, 3, or bc1 for mainnet addresses
- m, 2, or tb1 for testnet addresses
When using a lost wallet finder app to verify transactions, ensure the address formats correspond to the expected cryptocurrency network. Addresses that don’t follow standard formatting conventions warrant immediate suspicion.
Fake screenshots or transaction history
Scammers often use manipulated screenshots of wallet balances or transaction histories to establish false credibility or lure victims into scams.
Identifying fake Bitcoin wallet screenshots requires examining several elements. Inconsistent branding is a primary indicator—check for logos, colors, or fonts that differ from the official wallet’s design. Likewise, be wary of screenshots showing unusual features or functions not present in legitimate wallets.
If the screenshot includes a URL, verify its authenticity, as scammers frequently use similar-looking domain names to deceive users. Legitimate wallet screenshots typically display encryption indicators, such as a lock icon or HTTPS in the URL, whereas fraudulent ones may lack these security markers.
Using a trusted lost bitcoin wallet finder to cross-reference transactions against blockchain records provides an additional verification layer. These tools can help confirm whether transactions shown in screenshots actually exist on the blockchain, effectively revealing manipulation attempts.
Types of Fake Wallet Scams
Fraudsters have developed several sophisticated techniques to compromise Bitcoin wallets and steal cryptocurrency. Understanding these scam types is essential for protecting your digital assets and knowing when to employ a lost wallet finder tool for verification.
Phishing wallet apps
Phishing attacks begin with scammers creating convincing replicas of legitimate wallet interfaces. These counterfeit applications look remarkably similar to trusted platforms, often using lookalike domains with subtle character substitutions. For this reason, users download these apps believing them to be authentic.
Typically, victims receive emails or messages claiming to be from wallet providers, mentioning urgent security updates or verification requirements. Once installed, these applications harvest seed phrases and private keys, providing scammers with direct access to your funds.
Some attackers even use Webflow to create codeless phishing pages that target multiple crypto wallets simultaneously. This technique allows them to build authentic-looking interfaces without writing suspicious code that might trigger security software.
Malware-infected wallets
Malware targeting cryptocurrency comes in various forms, including trojans, infostealers, and cryptojackers. These malicious programs silently infiltrate your device and operate in the background, collecting sensitive wallet information.
Mars Stealer, for instance, sells on the dark web for under $200 and can bypass two-factor authentication on more than 40 different browser-based wallets. The malware spreads through torrent clients, peer-to-peer networks, and third-party download sites.
Other variants like SpyAgent malware distribute through text messages prompting downloads of seemingly legitimate apps. Once installed, these programs can view and steal saved image data, including screenshots of recovery phrases.
Impersonation of trusted brands
Brand impersonation has become increasingly sophisticated, with scammers creating fake browser extensions or applications that mimic popular wallets. They target well-known platforms because of their large user bases, making it easier to find potential victims.
Some fraudsters pose as customer support representatives, reaching out to users who post issues online. Eventually, they ask victims to “verify” their wallets by sharing seed phrases—a request that legitimate support staff would never make.
More advanced attacks employ deepfake technology to mimic the voice or appearance of well-known figures in promotional videos or livestreams. These sophisticated impersonations exploit users’ trust in familiar faces.
Clipboard hijacking and address spoofing
Perhaps the most insidious method is clipboard hijacking, where malware monitors your clipboard for cryptocurrency addresses and secretly replaces them with the attacker’s address. Given that wallet addresses are long hexadecimal strings, few people verify each character before confirming transactions.
Address poisoning (also called spoofing) involves creating “vanity addresses” that visually resemble legitimate ones. Scammers focus on matching the first and last few characters, knowing that most users only glance at these portions.
A lost wallet finder app can provide an additional security layer by verifying addresses before transactions, helping identify these subtle manipulation attempts.
How to Verify a Bitcoin Wallet
Verifying a Bitcoin wallet’s authenticity before use is your strongest defense against scams. With countless counterfeit options circulating online, thorough verification can mean the difference between secure transactions and devastating losses.
Check developer credentials and reviews
Reliable Bitcoin wallets come from reputable developers with established track records. First, examine the developer information in official app stores, looking for thousands of positive reviews and backing from recognized companies. Moreover, always download wallets exclusively from official websites or trusted app stores, never from third-party sources or links sent through messages.
Legitimate wallets typically display transparent development teams with verifiable backgrounds, throughout their documentation and websites. In contrast, fake wallets often hide behind anonymous entities or fabricated credentials.
Use blockchain explorers to confirm transactions
Blockchain explorers provide a transparent window into transaction histories and wallet activities. These powerful tools allow independent verification without relying on third parties.
To verify a wallet using a blockchain explorer:
- Visit trusted explorers like mempool.space or blockstream.info
- Paste the Bitcoin address into the search field
- Review the transaction history and current balance
- Cross-reference findings across multiple explorers for added security
Running your own self-hosted node offers the strongest verification, yet cross-checking results across several reputable explorers provides comparable assurance for most users.
Test with a small amount before full use
Sending a test transaction is an essential verification step, especially before transferring large amounts. This practice helps confirm that:
- The receiving address is correct
- Your network connection functions properly
- The wallet isn’t malicious or compromised
A successful test transaction provides valuable peace of mind, confirming your ability to both send and retrieve funds if needed.
Use a lost wallet finder app to cross-check
A lost wallet finder offers additional verification through address comparison against known databases. Legitimate lost wallet finder apps operate locally on your device without storing private information, minimizing security risks.
According to Bitget, as of June 2024, wallet recovery requests have increased by 30% compared to the previous year, highlighting growing awareness around secure verification methods.
Nonetheless, remember that no verification tool guarantees complete security—always combine multiple verification methods for maximum protection.
Using a Lost Wallet Finder to Stay Safe
Specialized tools called lost wallet finders have become essential in navigating the complex world of cryptocurrency security. These tools help protect your digital assets from scams that might otherwise drain your accounts.
What is a lost bitcoin wallet finder?
A lost wallet finder is specialized software designed to help users recover access to their cryptocurrency wallets. These tools use advanced algorithms to search for lost private keys, seed phrases, or wallet files. Since losing access to your wallet can mean permanently losing your funds, recovery solutions are crucial for cryptocurrency users. Some services provide expert support for users who have forgotten passwords or misplaced recovery phrases.
How lost wallet finder crypto tools work
Lost wallet finder tools typically function through several approaches. Initially, they scan for wallet addresses, mnemonic phrases, or cloud backups linked to your previous crypto activity. Some tools scan devices for remnants of wallet files, analyze backup data, or attempt to reconstruct lost credentials. Others help unlock wallets with partial information you still possess.
Best practices when using a lost wallet finder
When using wallet recovery tools, remember these essential safety practices:
- Never share your seed phrase with anyone
- Avoid websites that request your private keys
- Stay away from social media “wallet recovery” offers
- Be wary of services charging fees before providing services
For more info on secure wallet recovery methods and Flash BTC, visit https://realflashbtc.net.
Typically, legitimate recovery services will never ask for your private keys or your full seed phrase – consider this a major red flag. Although recovery tools can be helpful, prevention still remains your strongest strategy.
Conclusion
Navigating the cryptocurrency landscape requires constant vigilance against increasingly sophisticated scams. Throughout this guide, we’ve explored how fake Bitcoin wallets operate and the various techniques scammers use to steal your hard-earned digital assets. Therefore, applying multiple layers of verification before trusting any wallet application stands as your strongest defense against these threats.
Remember that legitimate wallets always come from verifiable sources, offer robust security features like 2FA, and maintain consistent address formats. Additionally, checking developer credentials, using blockchain explorers, and conducting small test transactions significantly reduce your risk of falling victim to scams. Unquestionably, prevention remains more effective than attempting recovery after funds have been stolen.
While lost wallet finder tools can help in certain situations, they should be approached with caution. Most importantly, never share your seed phrase or private keys with anyone claiming to offer recovery services. For more info on Flash BTC visit https://realflashbtc.net, where you can find additional resources about secure cryptocurrency management.
The cryptocurrency world offers tremendous opportunities, but also significant risks. As we’ve seen, scammers constantly develop new methods to target unsuspecting users. Though wallet security might seem complex initially, implementing the verification practices outlined in this guide will help safeguard your digital assets. After all, the few extra minutes spent verifying a wallet’s legitimacy can save you from potentially devastating financial losses.
Key Takeaways
Protecting your Bitcoin investments requires vigilance against sophisticated fake wallet scams that have already cost victims over $7.7 billion globally.
• Always download wallets from official sources only – avoid third-party links, SMS downloads, or social media promotions that bypass security screening • Verify essential security features like 2FA, proper address formats, and developer credentials before trusting any wallet application • Test with small amounts first and use blockchain explorers to independently verify transactions before making large transfers • Never share your seed phrase or private keys with anyone – legitimate services will never request this sensitive information • Use multiple verification methods including lost wallet finder tools to cross-check addresses against known scammer databases
Remember that cryptocurrency transactions are irreversible, making prevention your strongest defense. The few minutes spent verifying a wallet’s authenticity can save you from devastating financial losses that may be impossible to recover.
FAQs
Q1. How can I tell if a Bitcoin wallet is fake? Look for red flags such as unverified app sources, missing security features like two-factor authentication, mismatched wallet address formats, and suspicious screenshots or transaction histories. Always download wallets from official sources and verify developer credentials.
Q2. What should I do before using a new Bitcoin wallet? Before fully using a new wallet, check developer credentials and reviews, use blockchain explorers to confirm transactions, and test with a small amount of cryptocurrency first. These steps help verify the wallet’s authenticity and functionality.
Q3. Are there any tools to help verify Bitcoin wallet addresses? Yes, lost wallet finder tools can help cross-check addresses against known databases. These tools operate locally on your device and can provide an additional layer of security when verifying transactions.
Q4. What are some common types of fake wallet scams? Common fake wallet scams include phishing wallet apps, malware-infected wallets, impersonation of trusted brands, and clipboard hijacking. Be cautious of unsolicited messages, suspicious downloads, and requests for sensitive information.
Q5. How can I protect my cryptocurrency from wallet scams? To protect your cryptocurrency, always use wallets from official sources, enable all available security features, never share your seed phrase or private keys, verify transactions using blockchain explorers, and stay informed about the latest scam techniques. Regular security checks and updates are also crucial.